FBI and Indonesian Police Dismantle W3LL, the Phishing Platform Behind $20 Million in Fraud
In the first joint US-Indonesia operation targeting a cybercrime toolkit developer, authorities seized the W3LL phishing marketplace and detained its alleged creator after the platform was linked to more than 17,000 victims worldwide.
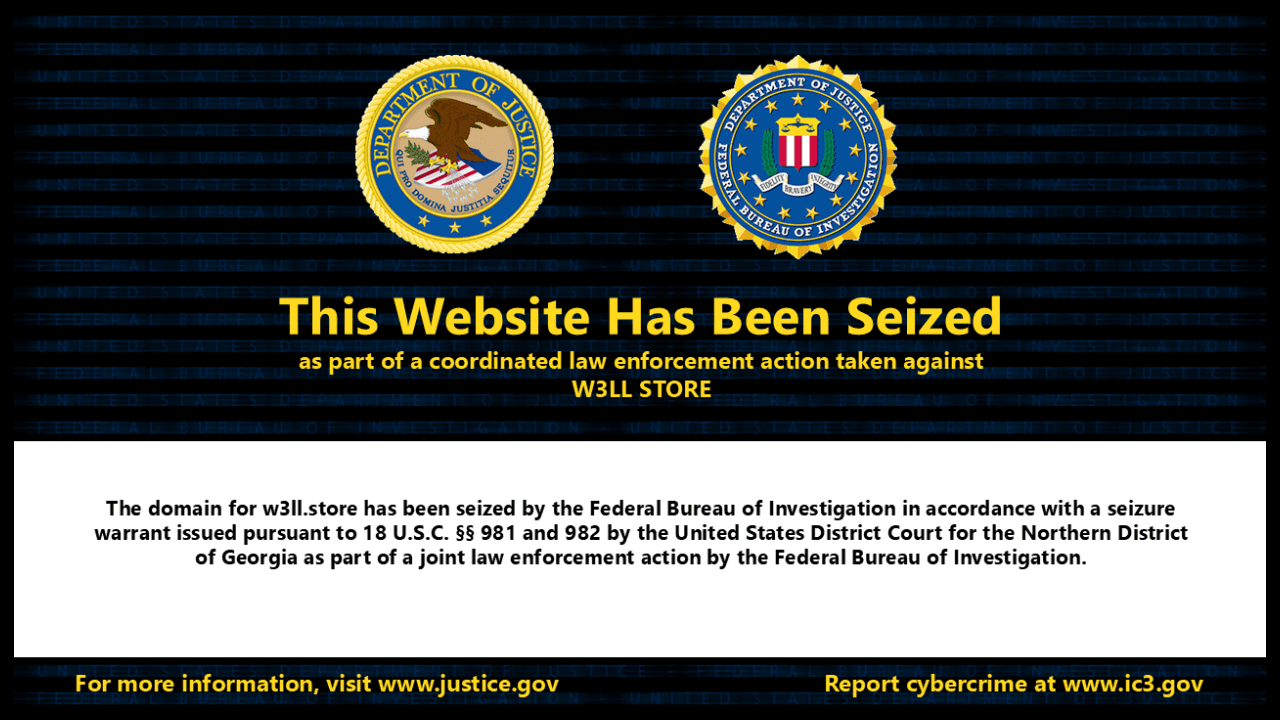
The FBI's Atlanta field office and the Indonesian National Police have dismantled W3LL, a phishing-as-a-service platform linked to more than $20 million in fraud attempts and over 17,000 victims worldwide. The joint operation -- the first coordinated enforcement action between the United States and Indonesia targeting a cybercrime toolkit developer -- resulted in the seizure of the w3ll.store domain and the detention of the platform's alleged developer in Indonesia.
Authorities seized the domain under a warrant issued by the US District Court for the Northern District of Georgia, pursuant to 18 U.S.C. §§ 981 and 982. Indonesian police detained the developer, identified only as G.L., who the FBI says personally collected and resold access to compromised accounts.
"This wasn't just phishing -- it was a full-service cybercrime platform," said FBI Special Agent in Charge Marlo Graham.
How W3LL Worked
For roughly $500, the W3LL phishing kit generated convincing replicas of legitimate login pages -- primarily targeting Microsoft 365 corporate accounts. Its most dangerous capability was an adversary-in-the-middle technique: rather than simply capturing passwords, W3LL intercepted session cookies in real time, allowing attackers to bypass multi-factor authentication entirely and maintain persistent access even after victims changed their passwords.
The platform operated as a full crime-as-a-service ecosystem. Beyond the core phishing kit, W3LL offered 16 additional tools -- SMTP senders, malicious link stagers, vulnerability scanners, automated account discovery instruments, and reconnaissance utilities -- all designed to work together in a complete business email compromise attack chain.
The Scale
Between 2019 and 2023, the W3LL Store marketplace facilitated the sale of more than 25,000 compromised accounts. Group-IB, the Singapore-based cybersecurity firm that first exposed the operation in September 2023, documented that W3LL tools were used to target approximately 56,000 corporate Microsoft 365 accounts between October 2022 and July 2023 alone. About 8,000 -- roughly 14 percent -- were ultimately compromised.
The FBI estimates the platform served roughly 500 threat actors across industries including manufacturing, IT, financial services, consulting, healthcare, and legal services.
A Platform That Wouldn't Stay Down
W3LL's developer had been active since at least 2017. When the W3LL Store marketplace shut down in 2023 -- partly in response to Group-IB's public exposure -- the platform migrated to encrypted messaging channels, where the tools were rebranded and actively marketed to the same criminal customer base.
The FBI noted that this operational resilience made the coordinated international enforcement action necessary. The seizure of infrastructure combined with the developer's detention aims to disrupt both the supply of phishing tools and the distribution of stolen credentials.