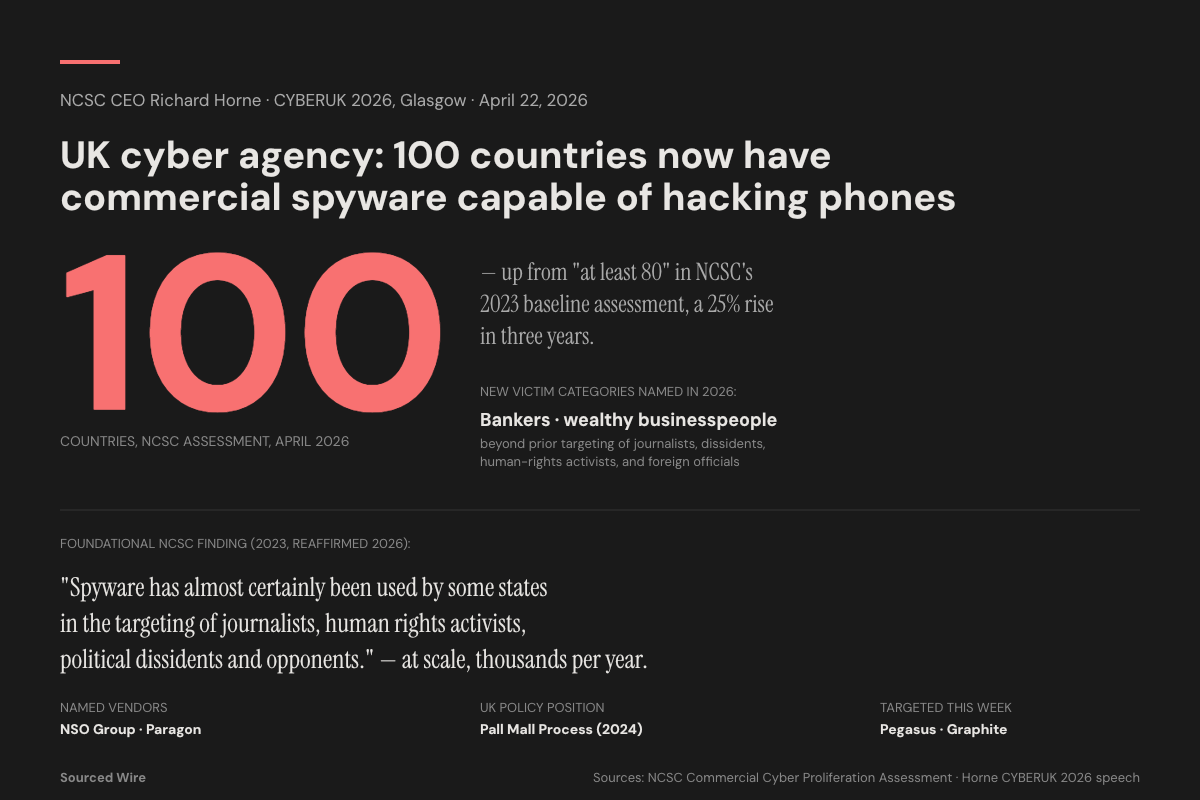
UK Cyber Chief: 100 Countries Now Have Commercial Spyware Capable of Hacking Phones, Up From 80 in Three Years
NCSC director Richard Horne, speaking at CYBERUK 2026 in Glasgow, said the commercial spyware market has grown 25% since the agency's 2023 baseline assessment and now targets bankers and wealthy businesspeople in addition to journalists, dissidents, and foreign officials.
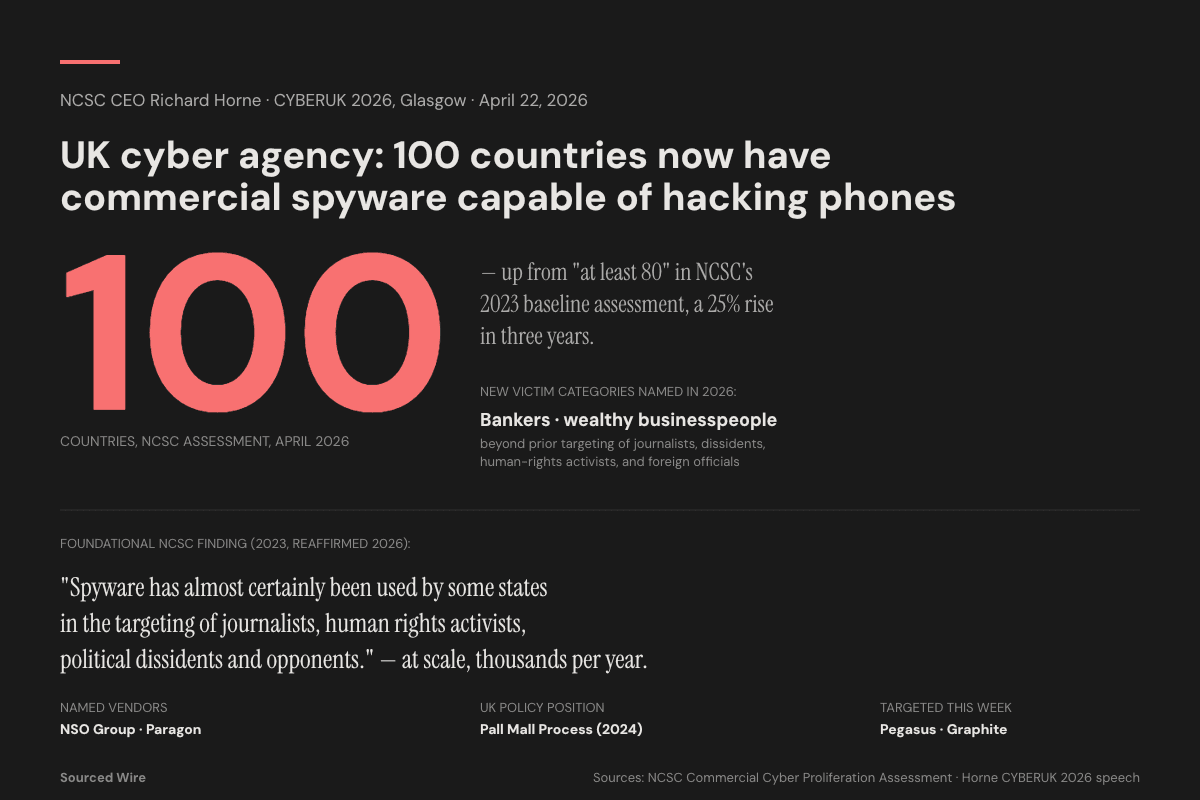
Richard Horne, director of the UK's National Cyber Security Centre, told the CYBERUK 2026 conference in Glasgow on Tuesday that approximately 100 countries now have access to commercial spyware capable of breaking into phones and computers — a 25% increase over the agency's 2023 baseline of "at least 80 countries," and a market that, in Horne's words, has begun to target a broader victim base than ever before.
The figure was disclosed in pre-released text of Horne's keynote speech at the conference, the UK government's flagship annual cyber-security event, held this year at the SEC in Glasgow alongside speeches from Security Minister Dan Jarvis and GCHQ Director Anne Keast-Butler. According to Horne's prepared remarks, the commercial spyware industry — once dominated by sales to law-enforcement and intelligence agencies — is now also being deployed against bankers and wealthy businesspeople, expanding well past the categories of victims (journalists, dissidents, foreign officials) the NCSC catalogued three years ago.
What the 2023 baseline said
The NCSC's foundational assessment on the topic — The Threat From Commercial Cyber Proliferation, published April 19, 2023 to coincide with that year's CYBERUK conference — judged that "at least 80 countries have purchased commercial cyber intrusion software, or spyware" over the prior decade. The assessment used the UK intelligence community's Probability Yardstick to issue several formal findings, including:
- That commercial spyware has "almost certainly been used by some states in the targeting of journalists, human rights activists, political dissidents and opponents and foreign government officials."
- That the targeting was "almost certainly happening at scale, with thousands of individuals targeted each year."
- That commercial intrusion products are "transformational" for states without an in-house cyber capability, granting them tools that "would otherwise take decades to develop."
Horne's CYBERUK 2026 update raises the country count by 20 and adds a new finding: that the customer base is no longer overwhelmingly state-connected. Targeting of private financial actors — bankers, wealthy businesspeople — represents a meaningful sectoral expansion of the commercial cyber-intrusion market beyond the espionage and counter-terror framings that dominated earlier assessments.
Vendors and tools in the public record
While the 2023 NCSC assessment did not name specific vendors, public reporting since has identified several Hacking-as-a-Service companies whose products fit the report's framing. Israeli firm NSO Group's Pegasus and Israeli firm Paragon's Graphite — both mobile-device spyware capable of zero-click compromise (no user interaction required) and of accessing messages, calls, photos, location, and the device's camera and microphone — are the products most widely documented as being deployed against the categories of victims the NCSC listed. Both firms have been the subject of US Commerce Department entity-list designations and US sanctions actions in recent years.
The UK's policy frame
The expanded NCSC figure lands in the middle of an ongoing UK-led international effort to constrain the commercial spyware market. In March 2024, the UK and France co-launched the Pall Mall Process, a multilateral initiative that has since produced a set of voluntary principles signed by 21 governments aimed at curbing the irresponsible proliferation of commercial cyber intrusion tools. Security Minister Dan Jarvis, in his own CYBERUK 2026 address on Tuesday, described commercial cyber proliferation as a "defining" challenge requiring international coordination, while flagging that the NCSC handled "over 200 nationally significant incidents" in the past year — many, per Horne, traceable to nation-state-linked actors.
The broader CYBERUK 2026 framing from Horne — that the UK faces a "perfect storm" of frontier-AI-enabled vulnerability discovery, geopolitical instability, and a rapidly diversifying commercial spyware market — was published as an NCSC press release on April 21, the day before the keynote. Horne's full transcript of the speech, including the 100-country update, is expected to appear on the NCSC's speeches page in the coming days.